
Security problem erasing Procurve switches
A investigation of some networks equipment manufacturers sanitization routines were performed early 2015 in Stril Networks lab.
The tests discovered it was possible to restore the whole configuration on HP Procurve switches even though the vendor's recommended factory reset method had been performed and the switch reported the switch was erased.
Further more it was also possible to restore not just the last configuration but also older historic configurations and manager passwords.
Technical details
The Procurve switches investigated had their flash system organized onto 4 major parts:
- Boot loader
- Primary image
- Secondary image
- NV File system
The NV file system was used by the Procurve switch to store configuration files, SSH crypto keys and manager passwords. Within the NV file system the files were organized sequentially as a linked list. When a new file had to be added, the previous files "NEXT" pointer was updated to link it into the new tail. A NEXT pointer of 0xffffffff indicated end of list.
If the file was to be erased the 16bit ACTIVE field was simple cleared (0x00ff -> 0x0000) . However the actual file contents was never erased and still intact in flash memory.
As such the files were never deleted and all historic versions of the file were still present in flash memory.
We tested several Procurve switches which all behaved equal so our guess is that this security flaw is present in all range of Procurve Switch Series.
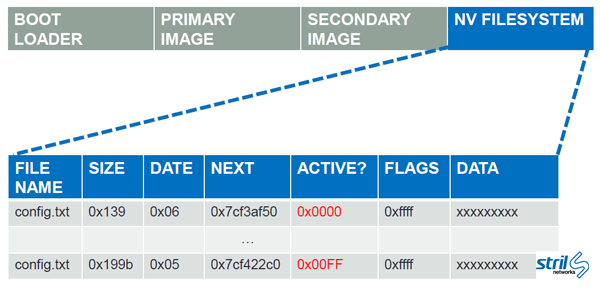 Procurve flash system layout.
Procurve flash system layout.
More technical details can be found in the full report:
![]() Sanitization of embedded network devices.pdf
Sanitization of embedded network devices.pdf
How to really erase Procurve switches
Stril Networks has developed the software tool Sanitty. It connects to the RS232 serial port of the switch, uses the boot loader debug mode to get access to the flash memory region. Then finds the NV file system region, investigates the linked list and erases all contents of the files. Byte by byte. With verification.
Contact us if you have Procurve switches in need of proper sanitization.
